The Accountant’s Tale: A Cautionary Story of a Phishing Attack and Incident Response
Introduction Jack was a highly competent accountant working for a small financial firm. He had been with the company for several years and was well-respected by his colleagues and superiors. One day, Jack received an email that looked like it was from one
The Rise of Finworth: A Fictional Tale of Ethics and Security in the Finance Industry
Disclaimer: The names of the companies mentioned in this story are fictional and any resemblance to real companies is purely coincidental. The purpose of this story is to illustrate the importance of ethics and security in the finance industry and is not intended
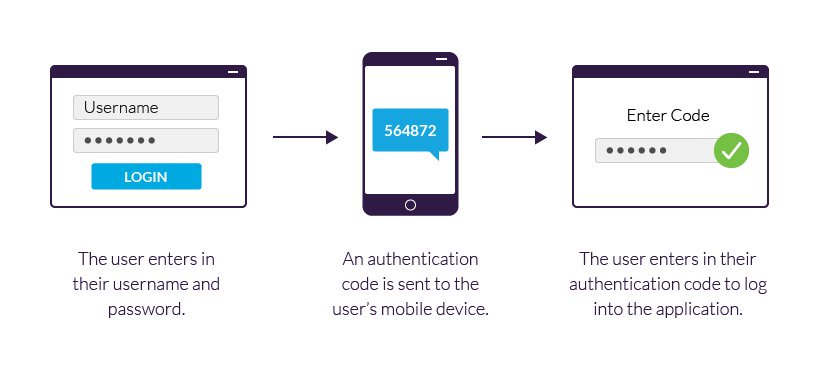
Two-Factor Authentication: Types, Benefits, and How to Choose the Right One for You
Introduction: Two-factor authentication (2FA) is a security process that requires users to provide two separate forms of identification in order to access their accounts. It adds an extra layer of protection beyond a password, ensuring that even if a password is compromised, the
Holiday Scams Can Ruin Your Season:
Tips for Spotting and Avoiding Phishing Attacks During the Holiday Season The holiday season is a time for joy and celebration, but unfortunately, it is also a time to be extra vigilant about scams. Every year, thousands of unsuspecting people fall victim to
“Protect Yourself from “Browser in the Browser” Attacks”
What You Need to Know and How to Protect Yourself Cyber threats are a constant concern for internet users. One type of attack you should be aware of is a “browser in the browser” attack. This involves using a malicious browser extension or
Malware in SVG?
We all know that malware is a serious threat to our online security. But did you know that malware can be hiding in plain sight – in the form of simple images? Recently, there has been a spate of reports about malware being
Phishing: Threat Actor’s Favourite Tool | C9 Lab
What is Phishing? Phishing is a simple and effective way to obtain sensitive information from unsuspecting victims, such as login credentials or financial information. In a phishing attack, the hacker creates a fake website or email that looks legitimate, and tricks the victim

Recent Comments