Two-Factor Authentication: Types, Benefits, and How to Choose the Right One for You
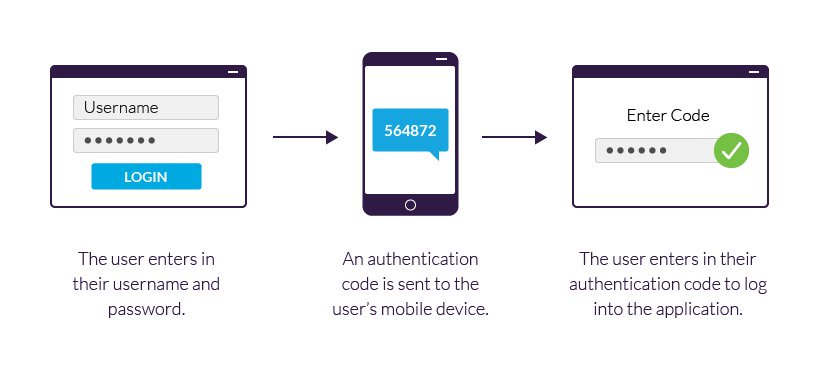
Introduction: Two-factor authentication (2FA) is a security process that requires users to provide two separate forms of identification in order to access their accounts. It adds an extra layer of protection beyond a password, ensuring that even if a password is compromised, the
Phishing Fiasco
“A well-informed employee is a company’s best defense against a phishing or cyber attack.” Cybersecurity Ventures The Real Story of How Jane Got Scammed This is how it started: The employees were settling into their workday on a typical Monday morning at a
The Importance of ISO 27001 for Business Growth
How Implementing an Information Security Management System Can Help Your Business Thrive As you know in today’s digital world, information is a valuable asset for businesses of all sizes. From customer data and financial records to proprietary processes and trade secrets, companies rely
Holiday Scams Can Ruin Your Season:
Tips for Spotting and Avoiding Phishing Attacks During the Holiday Season The holiday season is a time for joy and celebration, but unfortunately, it is also a time to be extra vigilant about scams. Every year, thousands of unsuspecting people fall victim to
Why SMBs Are High on Risk
Understanding the risks and taking steps to protect SMBs Small and medium-sized businesses (SMBs) are often targeted by cyber attacks and phishing attacks for a variety of reasons. These attacks can have serious consequences for SMBs, including financial losses, damage to reputation, and
“Protect Yourself from “Browser in the Browser” Attacks”
What You Need to Know and How to Protect Yourself Cyber threats are a constant concern for internet users. One type of attack you should be aware of is a “browser in the browser” attack. This involves using a malicious browser extension or
Malware in SVG?
We all know that malware is a serious threat to our online security. But did you know that malware can be hiding in plain sight – in the form of simple images? Recently, there has been a spate of reports about malware being

Recent Comments